Most businesses expect phishing attacks to arrive in their inbox. The latest one didn’t. On February 11, 2026, security researchers at Koi Security disclosed a first-of-its-kind attack: a malicious Microsoft Outlook add-in that operated inside Outlook itself, stealing over 4,000 Microsoft credentials, credit card numbers, and banking security answers—all while bypassing the email filters, endpoint protection, and URL scanning tools that businesses rely on every day.
The attack wasn’t sophisticated in the traditional sense. It was opportunistic, patient, and devastatingly simple. And it exploited something most organizations have never thought to check: the add-ins already installed in their Microsoft 365 environment.
How a Forgotten Tool Became a Weapon
The attack centered on “AgreeTo,” a legitimate calendar scheduling add-in that had been available through Microsoft’s official AppSource marketplace. At some point, the original developer abandoned the project and let the associated domain expire. An attacker quietly claimed that expired domain, then replaced the add-in’s content with a convincing fake Microsoft login page.
Because Outlook add-ins load dynamic web content from their registered domains, the phishing page appeared directly inside Outlook’s sidebar—within a trusted Microsoft process. The add-in’s existing “ReadWriteItem” permissions meant it could also read and modify emails. Stolen credentials, payment information, and security answers were exfiltrated in real time through a Telegram Bot API.
Microsoft removed the add-in on the day of disclosure. But the structural issue remains: Microsoft reviews add-ins at initial submission but does not continuously verify the content they serve after approval.
Why This Matters More Than a Typical Phishing Story
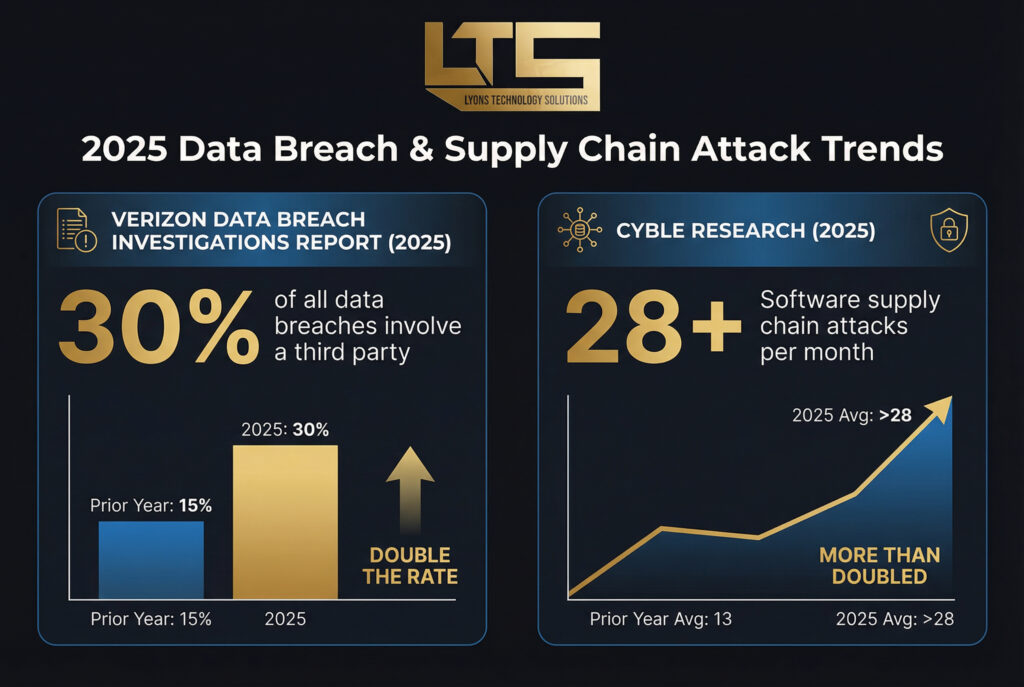
This incident is part of a broader trend that should concern every business running Microsoft 365. According to the 2025 Verizon Data Breach Investigations Report, 30% of all data breaches now involve a third party—double the rate from the prior year. Software supply chain attacks more than doubled in 2025, rising from an average of 13 per month to over 28, according to research from Cyble.
For small and mid-sized businesses, the risk is compounded by a visibility gap. A 2026 Panorays CISO Survey found that only 15% of security leaders have full visibility into their software supply chains. And for SMBs without dedicated security teams, that number is effectively zero.
The uncomfortable reality is that most businesses have never audited the add-ins, connected apps, or OAuth permissions in their Microsoft 365 environment. Tools get installed during onboarding, trials get forgotten, and permissions accumulate silently—creating exactly the kind of blind spot attackers exploit.
Strengthening Your Microsoft 365 Environment
The good news is that addressing this risk doesn’t require overhauling your technology stack. It starts with asking the right questions and building basic hygiene into your IT management:
Audit your add-ins and connected apps. Review what’s currently installed across your organization’s Microsoft 365 accounts. Remove anything that’s no longer actively used or recognized. A comprehensive cybersecurity strategy includes regular reviews of the tools connected to your environment—not just the threats trying to get in.
Restrict add-in permissions. Microsoft 365 allows administrators to control which add-ins users can install. Moving from an open policy to an approved-list model significantly reduces exposure to scenarios like AgreeToSteal.
Monitor for credential exposure. The 4,000+ credentials stolen in this attack will likely surface on dark web marketplaces. Dark web monitoring can alert you if your organization’s credentials appear in known breach databases, giving you the opportunity to act before stolen credentials are used.
Don’t assume “Microsoft” means secure. Cloud platforms like Microsoft 365 provide powerful infrastructure, but they operate on a shared responsibility model. Microsoft secures the platform; securing your environment within it is your organization’s responsibility—or your managed IT partner’s.
Take the Next Step
The AgreeToSteal attack is a reminder that the biggest security gaps aren’t always where you expect them. It’s not about having the wrong tools—it’s about not knowing what’s already running inside the tools you trust.
If your business relies on Microsoft 365 and you haven’t recently reviewed what’s connected to your environment, now is the time. A 15-minute conversation can help you understand where you stand and what steps make sense for your organization.
Schedule your complimentary IT consultation or call (517) 781-4868.





